When the curve goes vertical
For years we have lived with the sense that cybersecurity is a race: the attacker takes a step, the defense responds. The cat and mouse game. Sometimes the mouse wins, sometimes the cat. More or less balanced.
But something has changed.
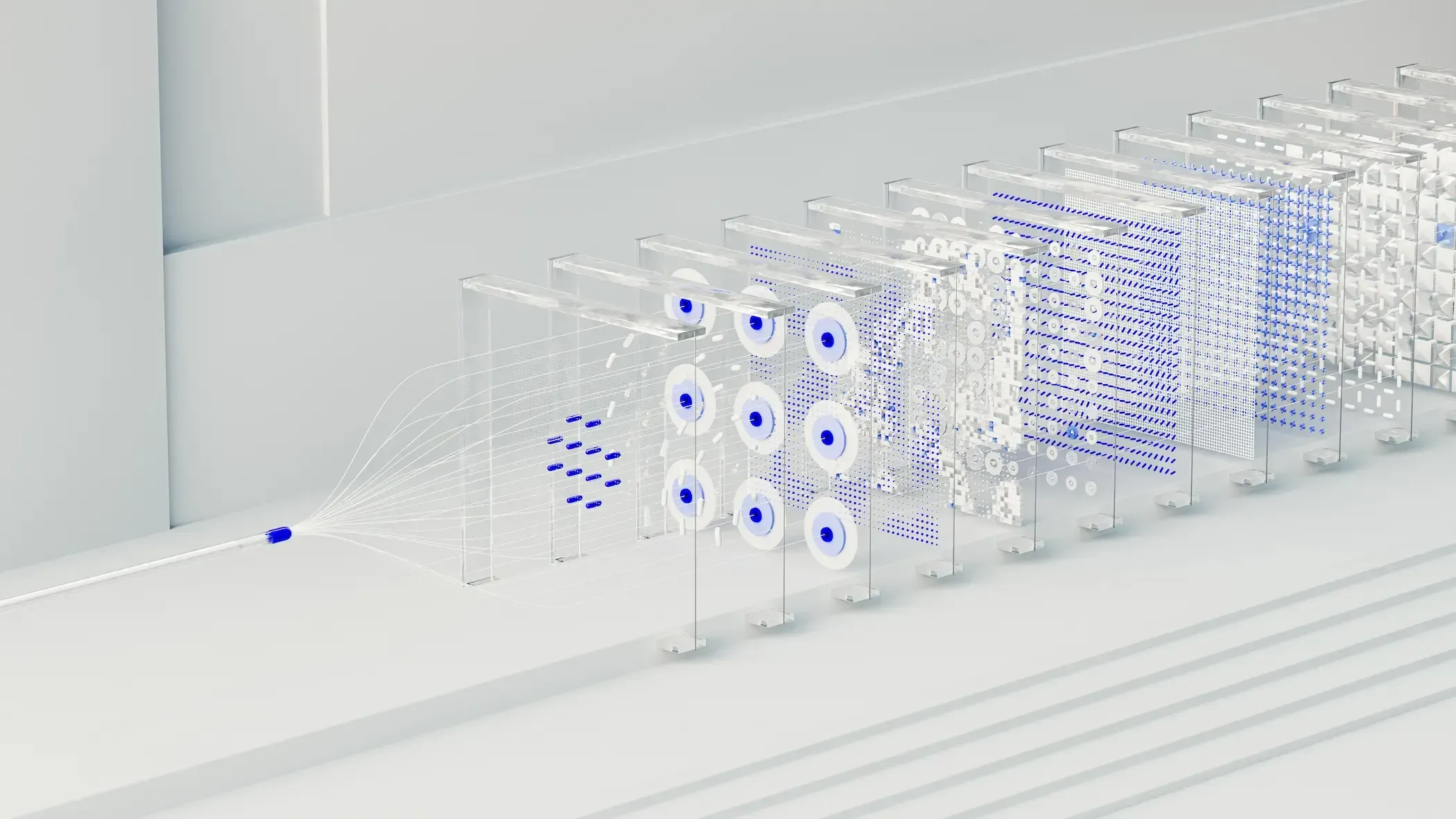
Since artificial intelligence burst onto the scene, the line stopped being a ramp and became a wall. A slope so steep that we can no longer climb at the same speed as the attackers. They are no longer running: they are flying. They iterate in seconds. And most of us are still deciding what kind of ropes to use for the climb.
Some numbers that stopped me in my tracks
A couple of weeks ago I attended the Barcelona Cybersecurity Congress, and some figures left me cold. Data that not only confirm what we already suspected, but amplify it with brutal clarity. According to figures shared by SoSafe:
- 88% of employees can be easily profiled from public information. This allows the creation of hyper-personalized spear phishing attacks that are difficult to detect even by experienced users.
- The cost of launching a spear phishing attack has dropped from 100% to 2%, thanks to generative artificial intelligence.
- And most worryingly: the click rate on AI-generated malicious emails has risen from 12% to 54%.
But what struck me most was not just the data, but the trend they reveal: attackers no longer need large resources, time, or even much technical knowledge. They only need access to an AI and a connection to a dark web forum.
And if we add that many organizations are integrating AI tools without reviewing their security, the result is an attack surface that grows every day without anyone watching.
AI is not only being used to attack: it is also becoming a new attack surface in itself.
Misconfigured models, logs that expose sensitive information, insecure prompts, systems without authentication… every new assistant, copilot, or automation without basic controls becomes an open door.
The offense has flourished
Generative artificial intelligence has made launching an attack easier, faster, and more profitable than ever. Anyone can generate perfect phishing emails, adapt malware in real time, or automate entire campaigns without writing a single line of code. Tools like WormGPT or FraudGPT, malicious versions of LLMs, are rented on the dark web for the price of a dinner.
Furthermore, we are seeing the emergence of autonomous agents capable of chaining offensive actions: scanning, identifying vulnerabilities, exploiting them, and extracting information, without human intervention. What once required days of preparation and technical knowledge can now be executed in minutes.
And meanwhile, on the defensive side…
The defense falls behind
Large companies can still play the game. They have security teams, budgets, and access to the latest tools. But SMEs, which represent over 90% of the European business fabric, are exposed.
Many still do not have an EDR, immutable backups, or even MFA enabled across all their access points. Not out of negligence, but because the pace of technology has become incompatible with their capabilities. Attackers are iterating every day; SMEs review their cybersecurity strategy once a year.
The result is predictable: SMEs are the new preferred target. They are easier, less noisy, and often hold data just as sensitive as a large corporation.
What can we do when we don’t have the same resources?
The key is not to try to scale with the same tools the attackers use. We cannot match their muscle, but we can play with the same intelligence.
And that is where the tipping point appears: start using AI to defend ourselves. I am not talking about expensive or inaccessible solutions. I am talking about the essentials:
- Hire managed services that monitor your systems 24/7.
- Automate responses to the most common incidents.
- Train your team with realistic AI-generated simulations.
- Apply least-privilege policies and review access regularly.
And above all, be properly covered.
I am not referring to the typical insurance that shows up when it is already too late. Today there are policies that go far beyond that: they respond when an attack happens, yes, but they also work with you to prevent it from occurring. They include prevention tools, technical advisory, and clear action protocols.
At Axyom we champion this type of coverage because we believe that real protection does not start with compensation, but with preventing the disaster in the first place. For many SMEs, it is the piece that completes the defensive system.
You don’t need a control tower, but you do need a plan
I have said it many times: most SMEs do not need an internal SOC.
But they do need a clear, up-to-date, and actionable strategy.
Today more than ever, cybersecurity is not just about protection: it is about speed.
The difference between surviving an attack and becoming a statistic lies in how many minutes it takes you to detect, contain, and respond.
We no longer have days. Sometimes, we only have an hour.
In summary
The offense flourishes when the technology curve goes vertical.
And today, that curve is practically a wall.
The good news is that you don’t need to be a large company to get started.
The bad news is that waiting is no longer an option.